How to check the integrity of files in the OS and the integrity of site files
Information is distributed by copying, downloading a file is also copying. Sometimes errors can occur during the copy process, due to which the copied object can be damaged - the consequences of such an event are obvious. In addition to errors, the file can be replaced or a code (usually malicious) added to it.
The question arises, how to check the integrity of the file ? For this, special data are used - hash sums. They allow, by comparing them, to determine whether a file has been modified or damaged. Hash sum is a simple sequence of characters that must be the same for two scanned objects - in this case, the file is intact. If the checksums do not match, the file is damaged. Hash data is represented using algorithms: MD5, MD4, MD2, SHA512, SHA384, SHA256, SHA1, etc.
How to find the hash-sum of a file ? To do this, you can use special programs, check the hash sum online on special sites, or use the built-in OS utility. Windows has the CertUtil utility for this. It is enough to type a command of the form and the hash-sum of the file will be shown: "certutil -hashfile path_to_file algorithm". In other operating systems, including mobile ones, as mentioned above, you can use programs.
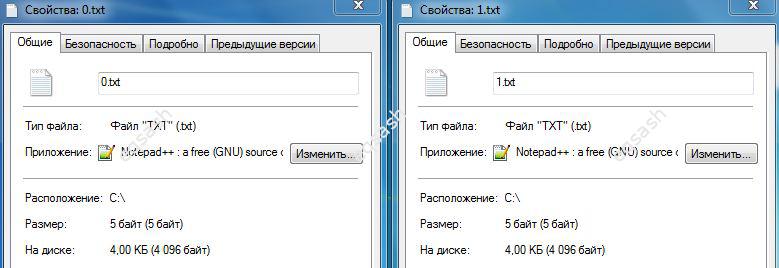
How to check the integrity of a file without hash ? To do this, you can simply try to open the properties of the two investigated files and compare their size byte. Of course, this method is not reliable, but it can be useful for a quick check of the file's integrity.
But there are other ways to check the integrity of files. For example, it is often asked, how to check the integrity of site files ? You can also check the integrity of files using web programming languages, for example, you can check hash sums in PHP . There are special functions for this. As a result, you can write a script that will automatically check all files on your hosting and display the hash of each file. You can save these values and then use a script to automatically compare the current hashes of the site files with the previous ones. This will find all file changes and thus check the integrity of site files . This method can be used to combat invisible injections of malicious or just extraneous code.
Latest articles
- 01.03.26IT / Уроки PHP Уроки простыми словами. Урок 3. Все операторы PHP с примерами, с выводом работы кода на экран.
- 28.02.26IT / Уроки PHP Уроки простыми словами. Урок 2. Типы данных в PHP с примерами.
- 27.02.26IT / Уроки PHP Уроки простыми словами. Урок 1. Коротко о языке веб-программирования PHP. Основы синтаксиса.
- 26.02.26IT / Database Errors when migrating from MySQL 5.6 to 5.7 and how to fix them - database dump import failed with an error or INSERT does not work. Disabling STRICT_TRANS_TABLES strict mode or using IGNORE
- 31.01.26IT / Misc Convert office files DOC, DOCX, DOCM, RTF to DOCX, DOCM, DOC, RTF, PDF, HTML, XML, TXT formats without loss and markup changes
 5685
5685